ExtremeWireless WiNG 5 WLAN
Renato.neves (Talk | contribs) |
Renato.neves (Talk | contribs) |
||
| Line 73: | Line 73: | ||
* Captive Portal Policy: select the previously created Captive Portal Policy (e.g.: "CP-SOCIAL-ID") | * Captive Portal Policy: select the previously created Captive Portal Policy (e.g.: "CP-SOCIAL-ID") | ||
* Select Encryption: Open | * Select Encryption: Open | ||
| + | |||
| + | == Configuring the Device Services == | ||
| + | |||
| + | You need to add the Captive Portal Policy previously created to the Device Services responsible to perform the RADIUS authentication, such as the Controller or Access Point (AP). | ||
| + | |||
| + | Select you device in "Configuration > Devices > Device Configuration" and go to the "Services" tab: | ||
| + | |||
| + | [[File:Wing5 device services.png|800px]] | ||
| + | |||
| + | Check the Captive Portal Policy previously created (e.g.: "CP-SOCIAL-ID"). | ||
Revision as of 17:46, 9 October 2015
Contents |
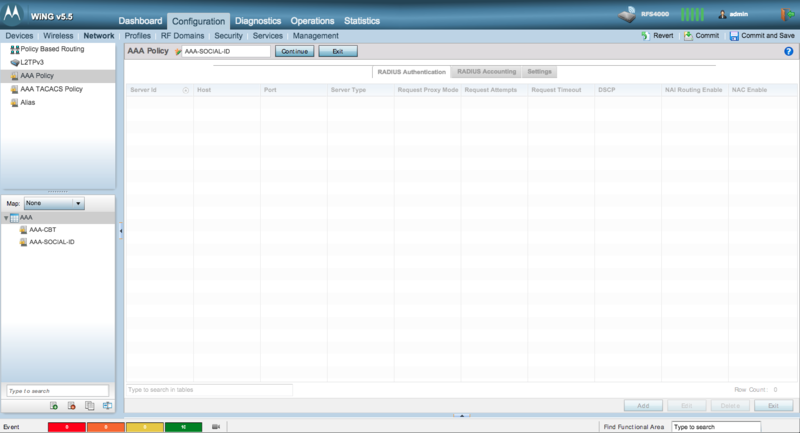
Configuring the RADIUS server
Configure the Social-ID RADIUS server by creating a new AAA Policy.
Go to "Configuration > Network > AAA Policy", click in the "Add" button and fill the AAA Policy name, such as "AAA-SOCIAL-ID":
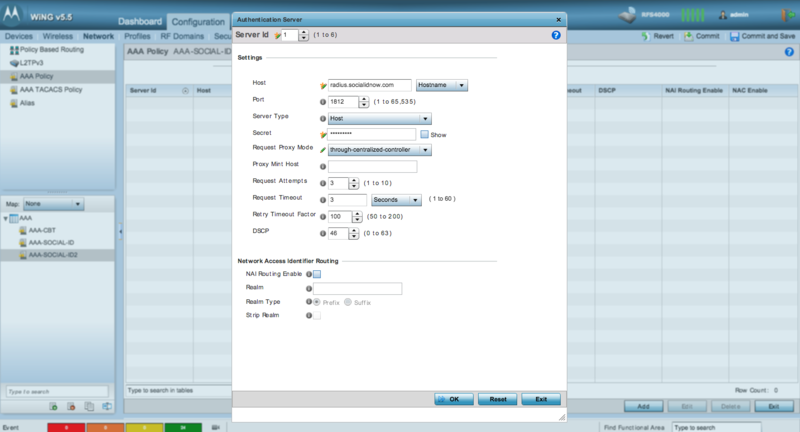
In the "RADIUS Authentication" tab click in the "Add" button and fill the following info:
- Host: radius.socialidnow.com (Hostname)
- Port: make sure that the chosen port is 1812
- Secret: the provided RADIUS client secret
- Request Proxy Mode: through-centralized-controller
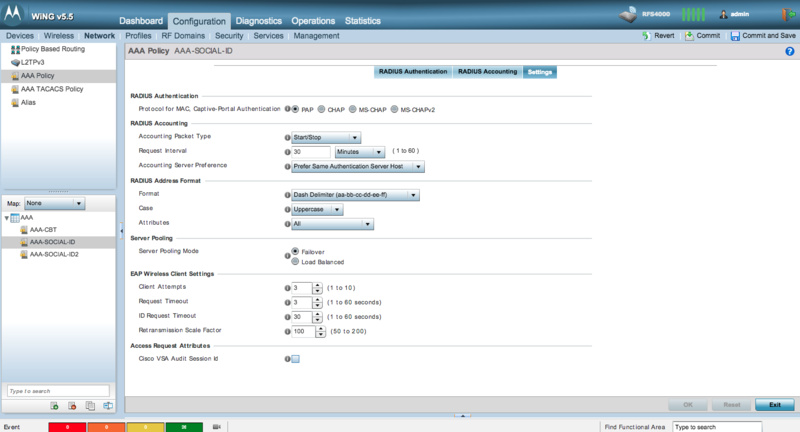
Click "OK" to save these settings and go to the "Settings" tab:
Double check these settings:
- RADIUS Authentication > Protocol for MAC, Captive Portal Authentication: PAP
- RADIUS Address Format > Attributes: All
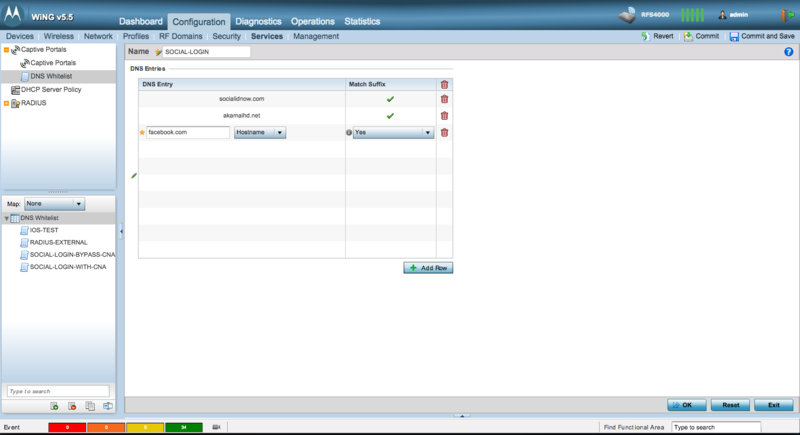
Configuring the DNS Whitelist
Go to "Configuration > Services > DNS Whitelist", click in the "Add" button and fill the "Name", such as "SOCIAL-LOGIN":
Create the DNS Entries according to Walled Garden for the Social Login URLs. Add each URL as a "Hostname" and Match Suffix as "Yes"
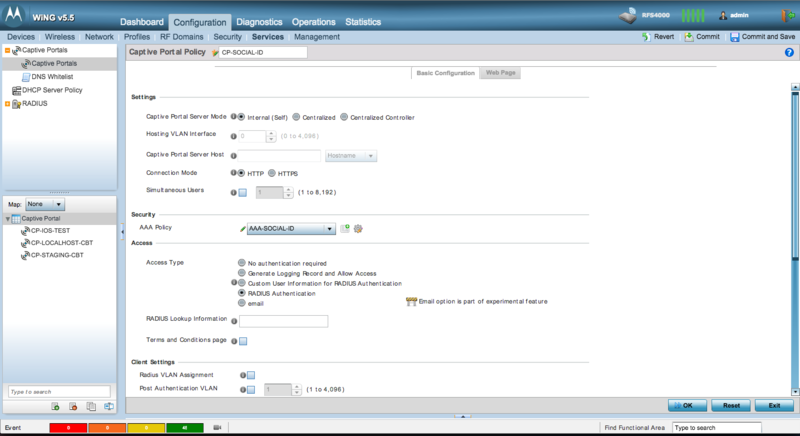
Configuring the Captive Portal
Go to "Configuration > Services > Captive Portal", click in the "Add" button and fill the Captive Portal Policy name, such as "CP-SOCIAL-ID":
Change the following settings in the "Basic Configuration" tab:
- Captive Portal Server Mode: Internal (Self) [you can select a more appropriate option if you prefer]
- AAA Policy: the previously AAA Policy created (e.g.: "AAA-SOCIAL-ID")
- Access Type: RADIUS Authentication
- DNS Whitelist: the previously DNS Whitelist created (e.g.: "SOCIAL-LOGIN")
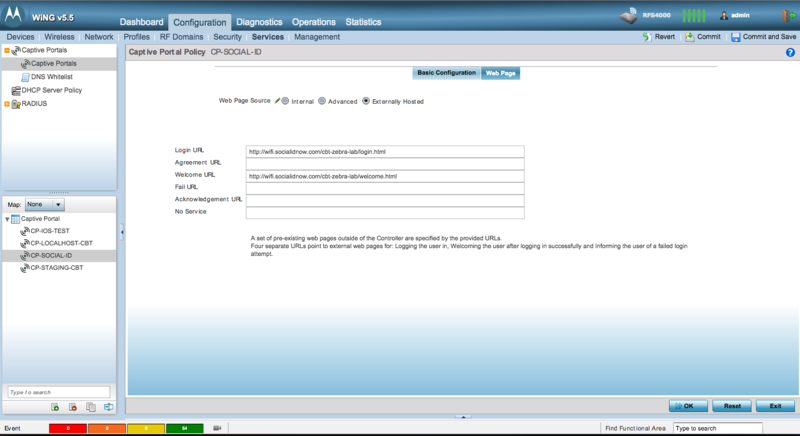
Click in "OK" to save the settings and go to the "Web Page" tab to configure the external captive portal:
Configure:
- Web Page Source: Externally Hosted
- Login URL: the provided captive portal login URL
- Welcome URL: the provided captive portal welcome URL
- Fail URL: the provided captive portal fail URL
You can fill the other URLs if you need also. Click in "OK" to save the settings.
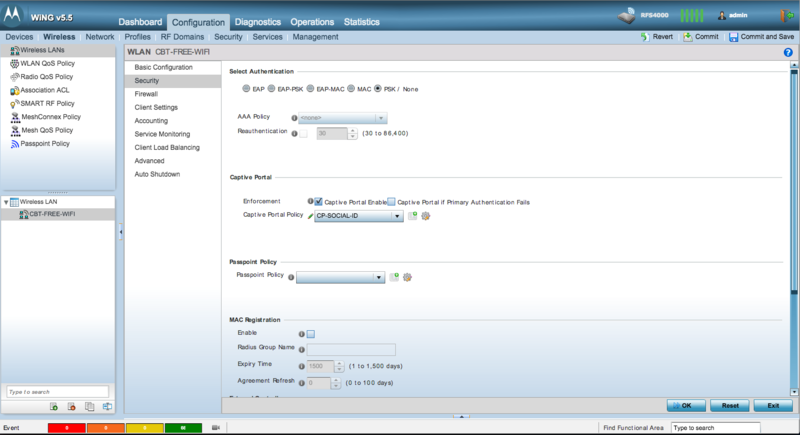
Configuring the Wireless LAN
Now you need to associate the Captive Portal previously created to the Wireless LAN. You need to have a Wireless LAN already created and configured in order to proceed with this step.
Select your Wireless LAN in "Configuration > Wireless > Wireless LANs" and go to the "Security" tab:
In order to provide Free Wi-Fi with Captive Portal enabled you need to set the following parameters:
- Select Authentication: PSK / None
- Enforcement: check "Captive Portal Enable"
- Captive Portal Policy: select the previously created Captive Portal Policy (e.g.: "CP-SOCIAL-ID")
- Select Encryption: Open
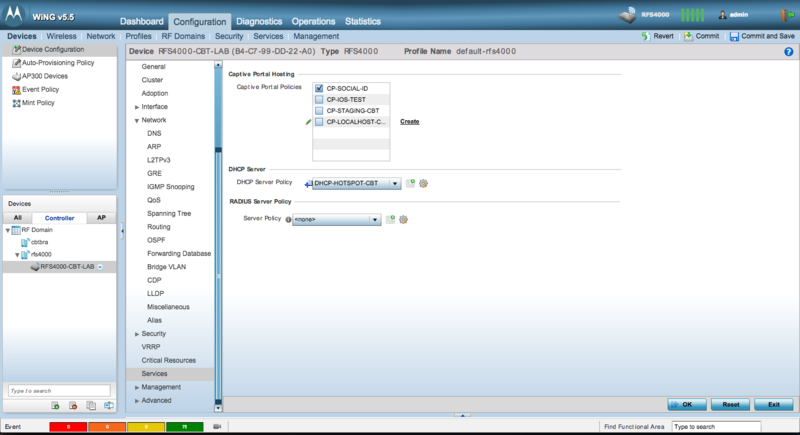
Configuring the Device Services
You need to add the Captive Portal Policy previously created to the Device Services responsible to perform the RADIUS authentication, such as the Controller or Access Point (AP).
Select you device in "Configuration > Devices > Device Configuration" and go to the "Services" tab:
Check the Captive Portal Policy previously created (e.g.: "CP-SOCIAL-ID").