Cisco Wireless LAN Controller (WLC)
Contents |
Introduction
This document outlines the configuration process for the Cisco WLC.
This process assumes that the Cisco WLC has been powered up and a basic IP configuration has been applied through the CLI to allow the administrator access to the Web-based User Interface.
Graphical User Interface
A browser-based Graphical User Interface is built into each controller, and allows up to five users to simultaneously browse management pages to configure and monitor operational status for the controller and its access points.
The controller GUI is supported for the following web browsers:
- Microsoft Internet Explorer, version 11 or a later version (Windows)
- Mozilla Firefox, version 32 or a later version (Windows, Mac)
- Google Chrome, version 38.x or a later version (Windows, Mac)
- Apple Safari, version 7 or a later version (Mac)
Logging into the GUI
Enter the controller’s IP address in your browser’s address bar (https://ip-address). When prompted, enter a System Name, a valid username (usually admin) and password, and click OK.
RADIUS
Radius Authentication
Click Security at the top of the User Interface and then AAA followed by Radius Authentication on the left-side menu bar. Configure the setting below:
- Auth Called Station ID Type: AP MAC Address:SSID
At the top of the page click new and complete as follows:
- Server IP Address: Insert RADIUS primary server IP here. You can check the IP for your region at our Captive Portal Configuration Page
- Shared Secret Format: ASCII
- Shared Secret: Insert Shared Secret provided by CoffeeBean here
- Confirm Shared Secret: Confirm Shared Secret here
- Port: 1812
- Server Status: Enabled
Click apply to save the newly configured settings.
Repeat the procedure and add a new entry for the RADIUS secondary server.
Radius Accounting
Click Radius Accounting on the left-side menu. Perform the setting below and then click Apply:
- Acct Called Station ID Type: AP MAC Address:SSID
At the top of the page, click New and set the following:
- Server IP Address: Insert RADIUS primary server IP here. You can check the IP for your region at our Captive Portal Configuration Page
- Shared Secret Format: ASCII
- Shared Secret: Insert Shared Secret provided by CoffeeBean here
- Confirm Shared Secret: Confirm Shared Secret here
- Port: 1813
- Server Status: Enabled
Repeat the procedure and add a new entry for the RADIUS secondary server.
Access Control Lists (ACL)
Preauthentication ACLs define the destinations a wireless visitor can reach before having to authenticate.
This may include a walled garden of local servers or other specific hosts that may be permitted access.
For the purposes of social logins, we must list domains of social media. On the Graphic User Interface, choose Security > Access Control Lists to open the ACLs page.
Note: if you wish to see if packets are hitting any of the pages configured on your ACL, select Enable Counters and then hit Apply, otherwise leave the box unselected.
Add a new ACL by clicking New. The Access Control List > New appears.
- Access Control List Name: Alphanumeric, max 32 characters
- ACL Type: IPv4 and IPv6 are supported
Click Apply to save.
Using Local APs
To the right of the ACL you’ve just created hover the blue arrow and click Add-Remove URL. In the URL String Name, add socialidnow.com.
Additionally, if you want to support social logins, you will need to add URL entries for each network you plan to support.
A regularly updated list of these domains can be found at our Walled Garden Page
Using FlexConnect Mode
Click on the ACL you’ve just created, then Add Rule > URL Rule at the top right.
In the URL box, add the domains one at a time, setting the Action to Permit each time. Refer to the URLs found at our Walled Garden Page
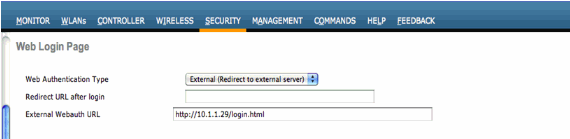
Web Authentication
Click Security > Web Auth > Web Login Page on the left and configure with:
- Web Authentication Type: External (redirect to external server)
- Redirect URL After Login: leave blank
- External Webauth URL: Insert captive portal login URL provided by CoffeeBean here
Click Apply to save.
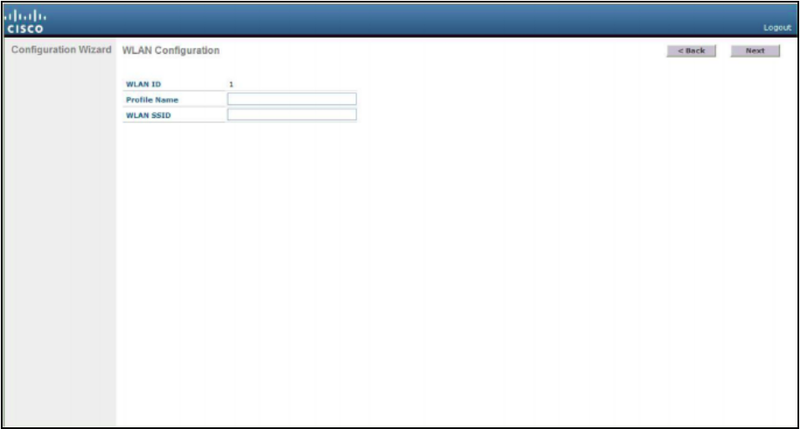
WLAN
A new wireless WLAN has to be defined in order to serve users. In this example we will be defining an SSID as Guest Wi-Fi.
Click WLAN at the top menu bar, then WLANS on the left. Click Create New > Go at the top right or edit an existing WLAN if you already have one.
If you’re creating a new WLAN, configure it with:
- Profile Name: Guest Wi-Fi
- SSID: Guest Wi-Fi (or whatever name you wish)
The Profile Name and SSID can be set to match the local preferences of your deployment. Click Apply to commit the changes.
Next, click the SSID profile to edit its settings
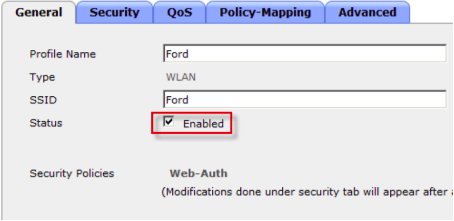
General
On the General tab:
- Status: Enabled
- Broadcast SSID: Enabled
- SSID: Guest Wi-Fi (or whatever name you wish)
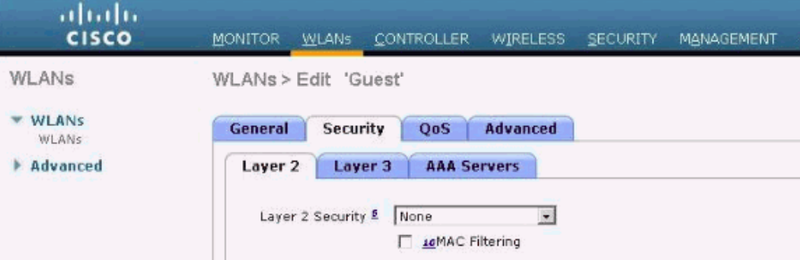
Security Layer 2
On the Security > Layer 2 tab:
- Layer 2 Security: None
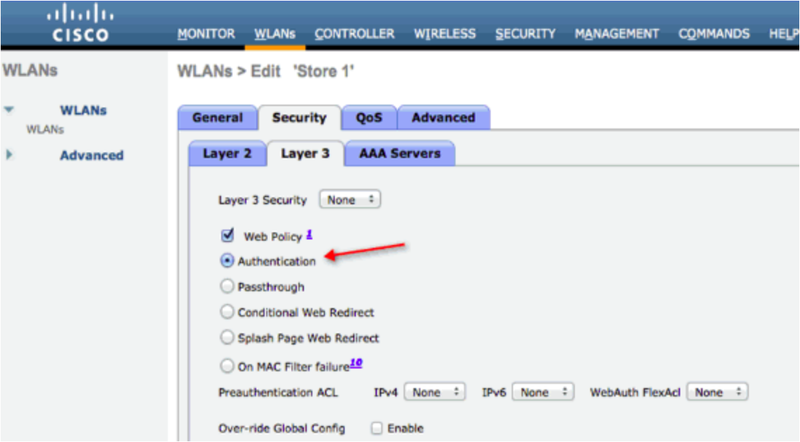
Security Layer 3
On the Security > Layer 3 tab:
- Layer 3 Security: Web Policy
- Authentication: Enabled
- Pre-Authentication ACL (if Local): Guest Wi-Fi
- WebAuth FlexACL (if FlexConnect): Guest Wi-Fi
- Override Global Config: Disabled
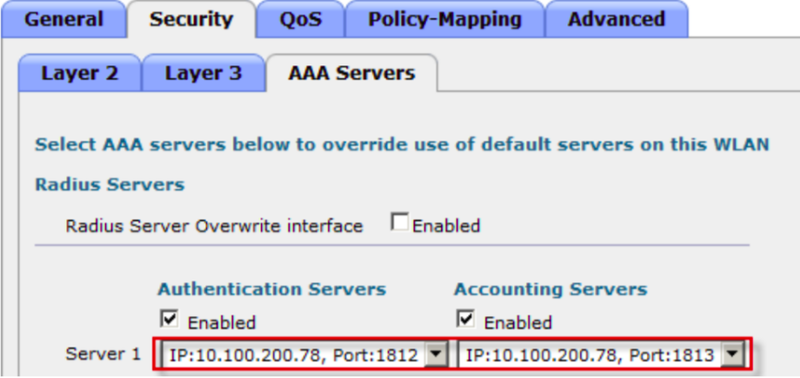
Security AAA Servers
On the Security > AAA Servers tab:
- Authentication Servers: Enabled
- Server 1: Select RADIUS authentication primary server created before
- Server 2: Select RADIUS authentication secondary server created before
- Accounting Servers: Enabled
- Server 1: Select RADIUS accounting primary server created before
- Server 2: Select RADIUS accounting secondary server created before
- Interim Update: Enabled
- Interim Interval: 600
- Authentication priority order for web-auth user
- Not Used: LOCAL, LDAP
- Order used for Authentication: RADIUS
Management
Next, click Management at the top then HTTP-HTTPS on the left. Configure with:
- WebAuth SecureWeb: Disabled
- HTTPS Redirection: Disabled
Click Controller at the top then interfaces on the left. Configure with:
- IP Address: Set your IP address (e.g. 192.0.2.1)
Click Apply to save and then Save Configuration at the top right.
Note: for all the features to work, your controller must be rebooted.
Customer Parameters
The summary of customer specific parameters is:
Basic Settings
- Redirection URL: the provided captive portal login URL
- RADIUS (primary and secondary)
- Authentication
- Server IP Address: You can check the IP for your region at our Captive Portal Configuration Page
- Shared Secret: Provided by CoffeeBean
- Port: 1812
- Accounting
- Server IP Address: You can check the IP for your region at our Captive Portal Configuration Page
- Shared Secret: Provided by CoffeeBean
- Port: 1813
- Authentication
- Access Control List: A regularly updated list of these domains can be found at our Walled Garden Page
- Captive Portal
- External Webauth URL: Captive Portal Login URL provided by CoffeeBean