Mikrotik RouterOS
The following guide was created using a Mikrotik network with the following components:
- Router: Mikrotik RouterBoard 450G
- Firmware: 3.22
- RouterOS: v6.23
Contents |
Requirements
You need to have a Mikrotik RouterBoard with Internet access already configured.
You can reset your RouterBoard and connect the cable with Internet access at the ethernet gateway port (ether1-gateway).
By default, the RouterBoard is configured with automatic address acquisition, so it will get the IP and Gateway from your Internet cable connection and will set up a DHCP Client also.
This guide was created using the WebFig configuration interface, but you can apply the same settings using the Winbox.
Interfaces
By default, the RouterBoard 450G comes with 5 ports and the following interfaces:
- ether1-gateway
- ether2-master-local
- ether3-slave-local
- ether4-slave-local
- ether5-slave-local
In this guide, we'll create a new interface (bridge-hotspot) and associate one of the slaves interface to the bridge.
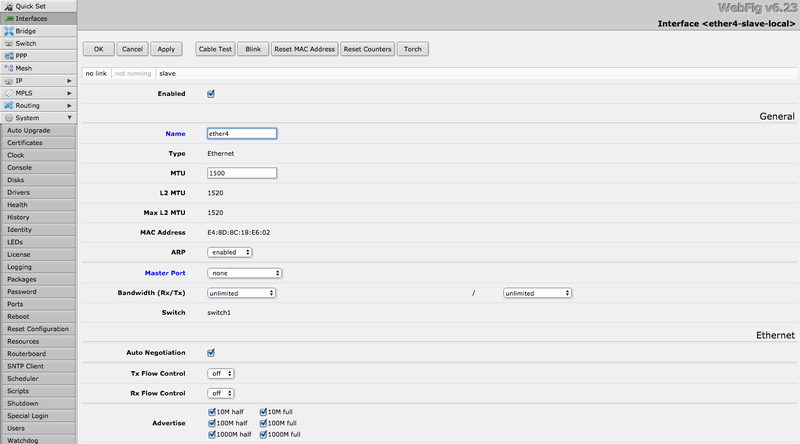
Ethernet
Go to Interfaces and edit one of the interfaces (e.g. ether4-slave-local). Change the following options:
- Name: ether4
- Master Port: none
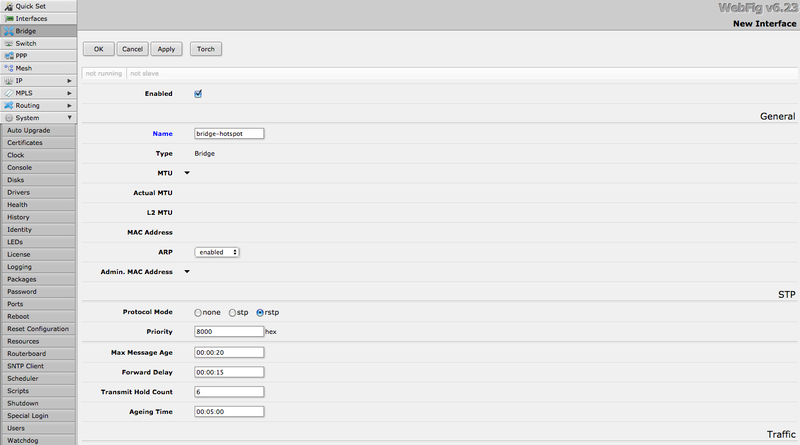
Bridge
Go to Bridge and click in "Add New". Set the following options:
- Name: bridge-hotspot
Bridge Port
Now you need to associate the Ethernet interface to the bridge.
Go to Bridge > Ports tab and click in "Add New". Set the following options:
- Interface: ether4
- Bridge: bridge-hotspot
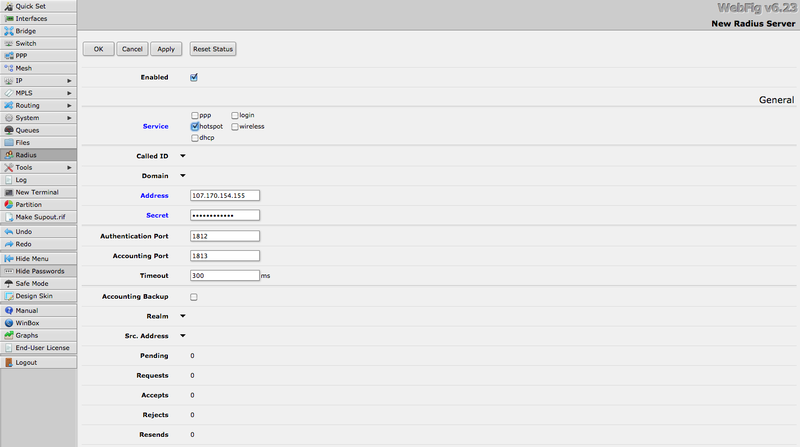
Radius
Go to Radius and click in "Add New". Set the following options:
- Enabled: checked
- Service: Hotspot
- Address: the RADIUS server IP according to your environment/region
- Secret: the provided RADIUS client secret
- Authentication Port: 1812
- Accounting Port: 1813
- Timeout: 2000 ms
Repeat the procedure for the secondary RADIUS server.
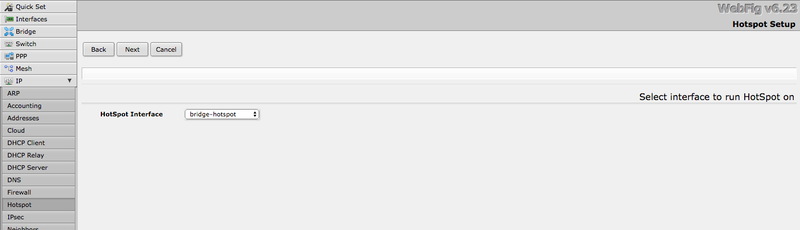
Hotspot
Go to IP > Hotspot.
Mikrotik offers a wizard (Hotspot Setup) to create almost all resources related to the Hotspot.
Hotspot Setup
Click in "Hotspot Setup".
Choose the "bridge-hotspot" as the "Hotspot Interface":
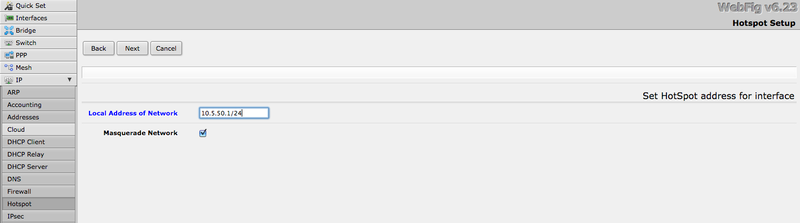
Set "Local Address of Network" as 10.5.50.1/24:
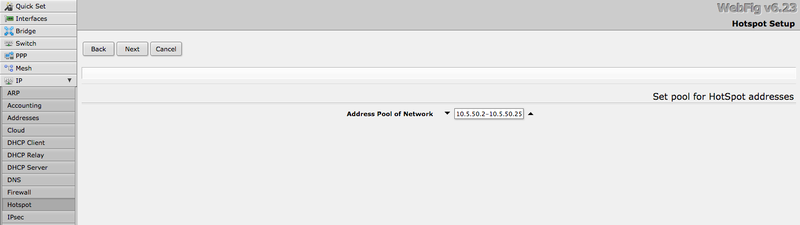
Let the default value (10.5.50.2-10.5.50.254) for "Address Pool of Network":
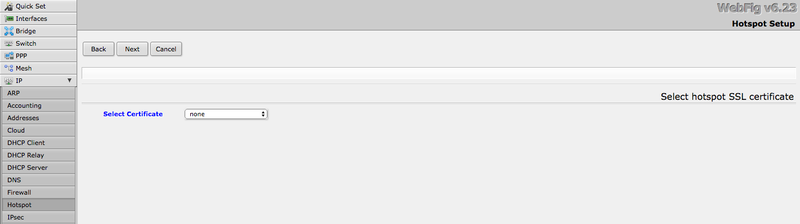
Set "Select Certificate" as "none":
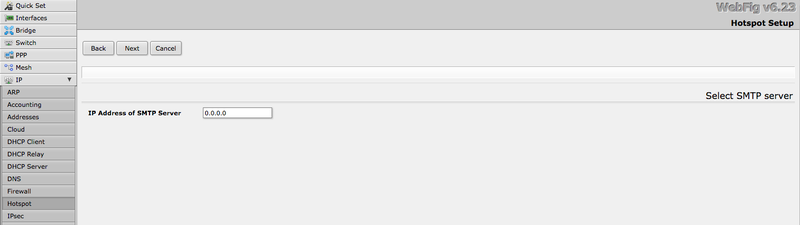
Set the "IP Address of SMTP Server" as "0.0.0.0":
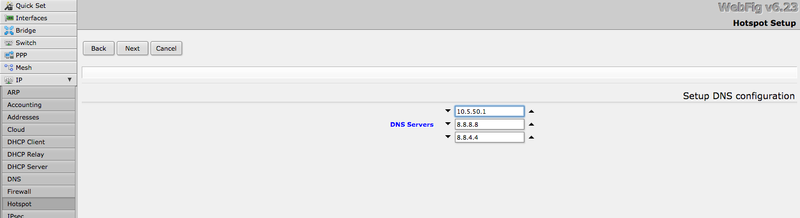
Set the DNS servers:
- 10.5.50.1
- 8.8.8.8 (optional)
- 8.8.4.4 (optional)
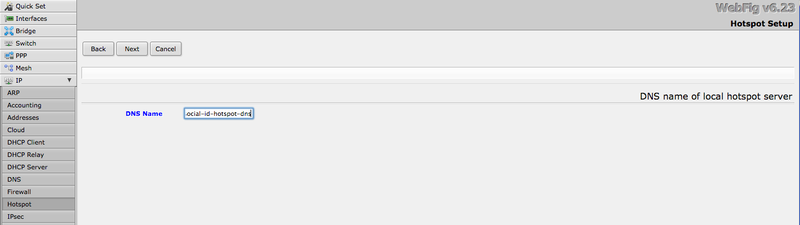
Set the "DNS Name" as "social-id-hotspot-dns":
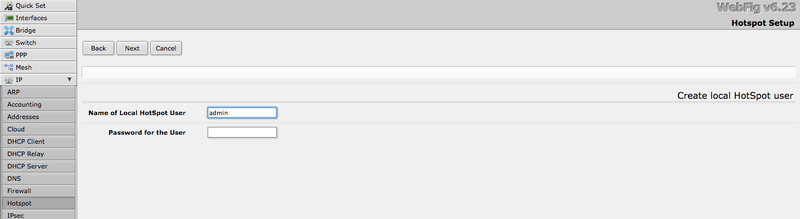
And create the default Hotspot user:
You can remove this user later.
Now you have your Hotspot resources created. You'll need to change some settings in the following steps.
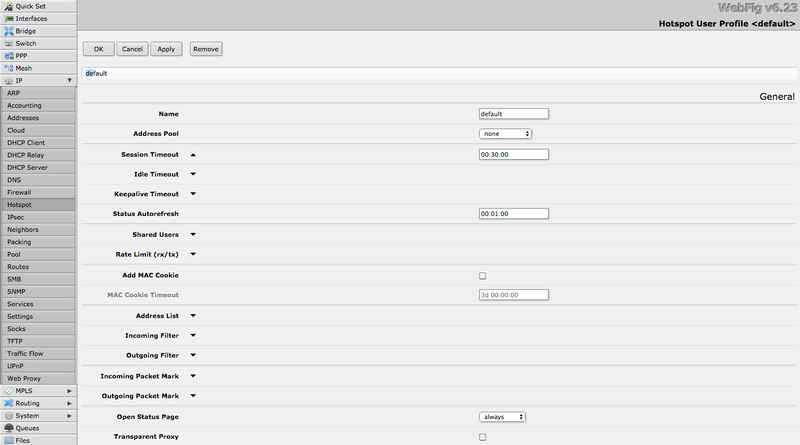
User Profile
Go to IP > Hotspot > User Profiles. Edit the default entry and change the following options:
- Session Timeout: 00:30:00
- Idle Timeout: clear this entry
- Shared Users: clear this entry
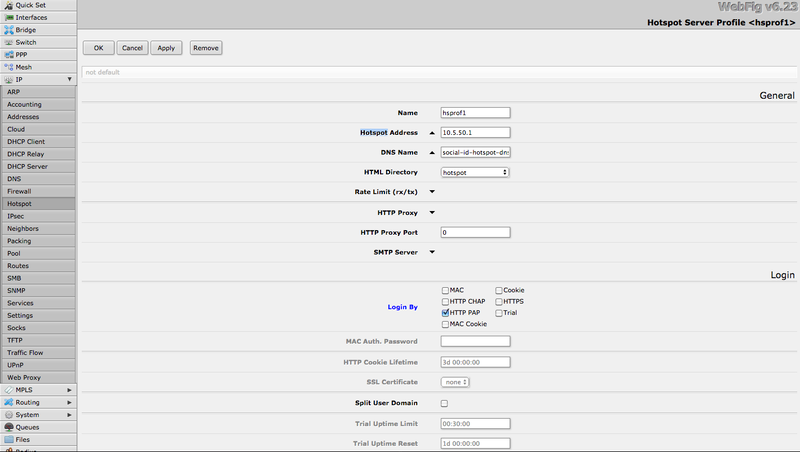
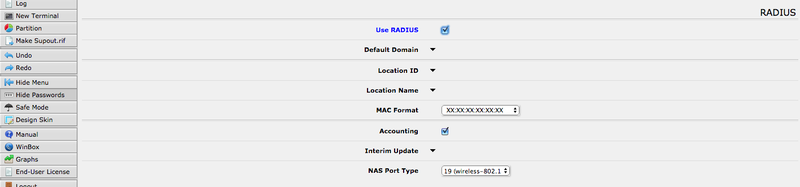
Server Profile
Go to IP > Hotspot > Server Profiles. Edit the hsprof1 entry and change the following options:
- Login By: check only "HTTP PAP" option
- Use RADIUS: checked
- MAC Format: XX:XX:XX:XX:XX:XX (default option)
- Accounting: checked (default option)
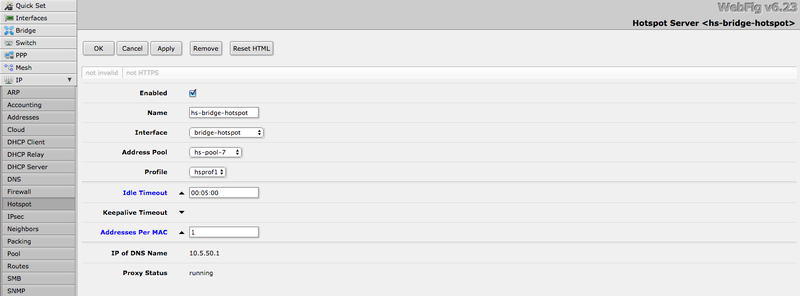
Hotspot Server
Go to IP > Hotspot > Servers. Edit the hs-bridge-hotspot and change the following options:
- Idle Timeout: set the desired timeout (e.g.: 00:05:00)
- Addresses Per MAC: 1
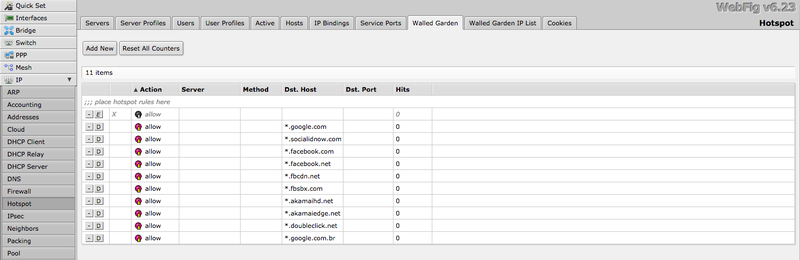
Walled Garden
Allow CoffeeBean Platform URLs and social network URLs by configuring the Walled garden.
Go to IP > Hotspot > Walled Garden. For each Walled Garden for the Social Login domain you need to use, create an entry in the Walled Garden.
For example, to add *.socialidnow.com, click in "Add New" and set the following options:
- Dst. Host: *.socialidnow.com
At the end, you'll have something like this:
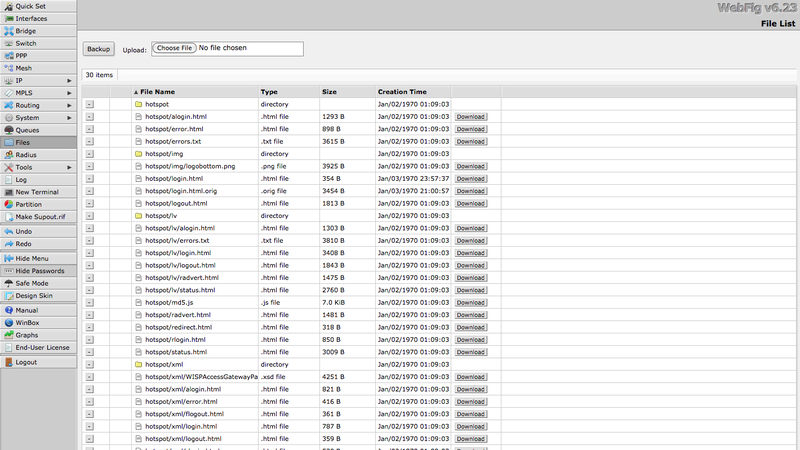
Files
When you create a hotspot on Mikrotik, it automatically adds all the files and directories, creating an "internal" portal hosted on Mikrotik, so when a client connects to the network, it is redirected to this portal.
If you lose this files, you can recreate them by going into IP > Hotspot > Hotspot Server, click to edit your server and then click in the button "Reset HTML". The file structure is similar to this:
The CoffeeBean Wi-Fi portal is an external portal, in the cloud. So you need to redirect the internal login page to the external one hosted by CoffeeBean.
You must replace your hotspot/login.html file by:
<html>
<head>
<title>Login</title>
<meta http-equiv="refresh" content="0; url=http://wifi.socialidnow.com/portals/<portal-name>/auth?client_mac=$(mac)&client_ip=$(ip)&login_url=$(link-login-only)" />
<meta http-equiv="pragma" content="no-cache">
<meta http-equiv="expires" content="-1">
</head>
<body>
</body>
</html>
Where <portal-name> must be replaced by your portal name.
To replace this file you can use a FTP client to connect to Mikrotik appliance.
Venue Customization
Mikrotik does not provide a parameter to identify which AP is being used, so there is no way to automatically detect the current venue. If you need the venue information to perform any customization or for reporting, you may want to use a custom flow to detect it.
The simplest way to achieve it is to map a Mikrotik variable (e.g. the "server-name") to the venue name and update the portal template as described in the Captive Portal Customizations - Venues page.
You'll also need to update the hotspot/login.html code as shown below to also add the Mikrotik variable that holds the venue name:
<html>
<head>
<title>Login</title>
<meta http-equiv="refresh" content="0; url=http://wifi.socialidnow.com/portals/<portal-name>/auth?client_mac=$(mac)&client_ip=$(ip)&login_url=$(link-login-only)&venue_name=$(server-name)" />
<meta http-equiv="pragma" content="no-cache">
<meta http-equiv="expires" content="-1">
</head>
<body>
</body>
</html>
Wireless Gateway
Mikrotik offers products in the Wireless and Ethernet Routers categories, both running RouterOS.
If you have a Wireless appliance, you can just configure the Wireless Interface to the Bridge, and your Wireless network will be ready to manage user authentication by the Hotspot server.
If you have an Ethernet Router, you can use it as a gateway to manage Hotspot services. Connect an AP from any vendor to the configured Hotspot Interface, so all clients connected to the AP will be required to authenticate through Mikrotik Hotspot Server. To create this guide we set up a Cisco Aironet AP, with open authentication, and connected to the Mikrotik's ether4 port, that is a slave for the hotspot bridge.
Security
Don't forget to follow some simple security guidelines:
- Set a strong password for any admin user.
- Review firewall rules (IP > Firewall).