Ubiquiti UniFi
This guide describes the configuration steps to enable an external captive portal in the Ubiquiti UniFi.
This guide was created using the following components:
- Controller: UniFi Network Controller 5.10.21 for Debian/Ubuntu Linux and UniFi Cloud Key
- AP model: UniFi UAP
Contents |
Requirements
This guide outlines the configuration process for the Ubiquiti Networks UniFi Access Points.
This process assumes that the device has been powered up and a basic IP configuration has been applied through the CLI to allow the administrator access to the Web-based User Interface.
Graphical User Interface
A browser-based Graphical User Interface is built into each controller, and allows users to browse management pages to configure and monitor operational status for the controller and its access points.
After setting up the IP, the controller GUI will be available through port 8443 by default.
Network Configuration
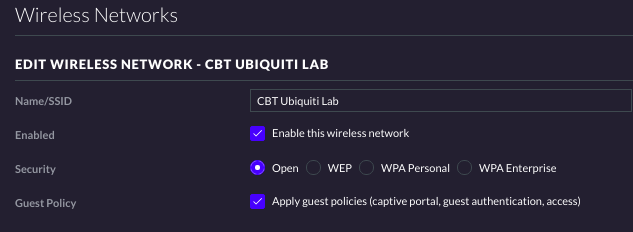
On the browser-based GUI, head to Settings and then on Wireless Networks. Either add a new network or edit the one you have already created. Perform the following settings:
- Name/SSID: NameOfYourNetworkHere
- Enabled: Check Enable this wireless network
- Security: Open
- Guest Policy: Check Apply guest policies (captive portal, guest authentication, access)
RADIUS Server
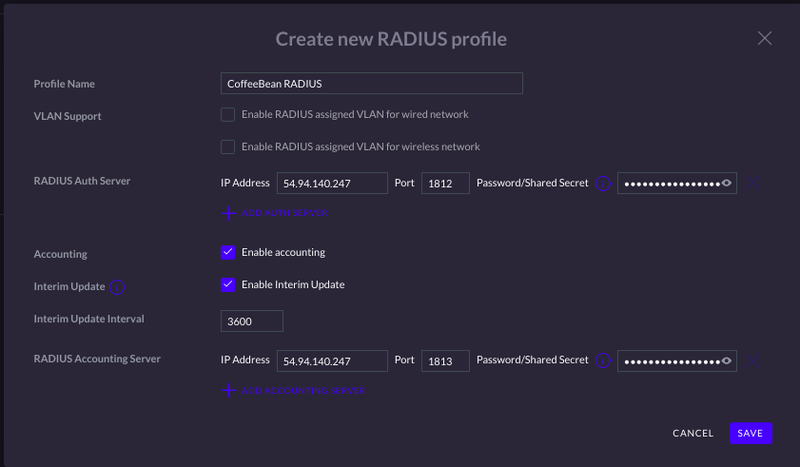
In the left-side menu options, select Profiles and then click on Create New Radius Profile. Fill in the fields as shown below:
- Profile Name: Name your RADIUS Profile here (e.g. “CoffeeBean RADIUS”)
- VLAN Support: Leave unselected
- RADIUS Auth Server (add primary and secondary servers)
- IP Address: The RADIUS IP will depend on your environment/region. You can check the IP for your region at our Captive Portal Configuration Page
- Port: 1812
- Password/Shared Secret: Use the Shared Secret provided by CoffeeBean
- Accounting: Check Enable Accounting
- Interim Update: Check Enable Interim Update
- Interim Update Interval: 3600
- RADIUS Accounting Server: (add primary and secondary servers)
- IP Address: The RADIUS IP will depend on your environment/region. You can check the IP for your region at our Captive Portal Configuration Page
- Port: 1813
- Password/Shared Secret: Use the Shared Secret provided by CoffeeBean
Guest Control
In the left-side menu options, select Guest Control to start customizing your user’s flow in regards to authentication.
Guest Policies
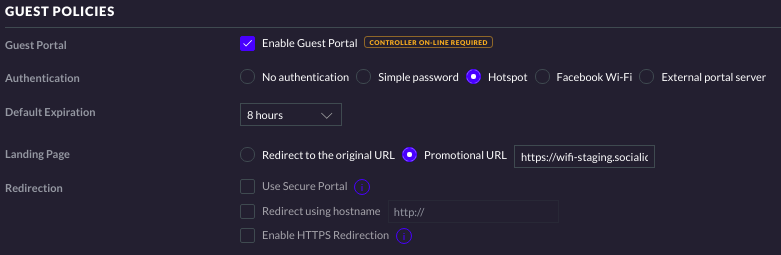
Under the Guest Policies menu, make the following selections:
- Guest Portal: Check Enable Guest Portal
- Authentication: Hotspot
- Default Expiration: User-defined
- Landing Page: Select Promotional URL - This URL will be provided by CoffeeBean
- Redirection: Leave unselected
Portal Customization
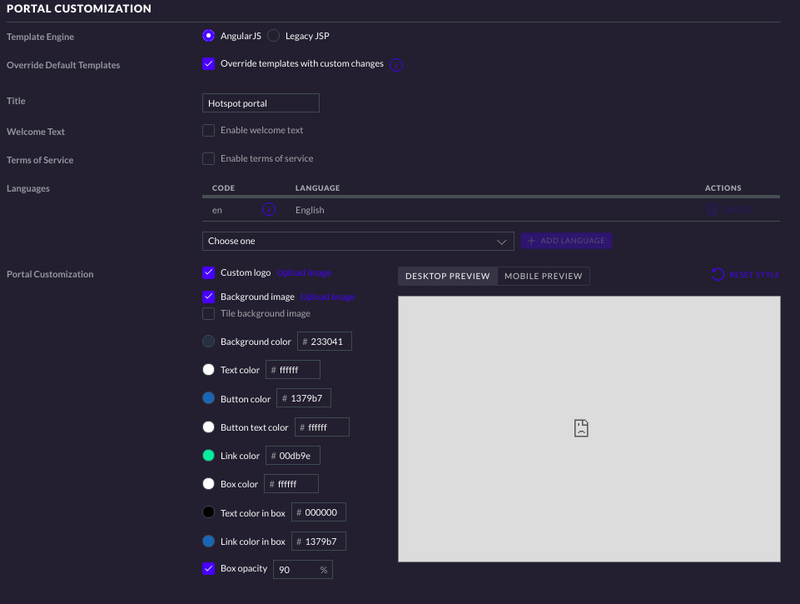
Under this menu, make the following selections:
- Template Engine: AngularJS
- Override Default Templates: Check Override templates with custom changes
- Title: Name your portal here
The rest of the settings here can be left as default.
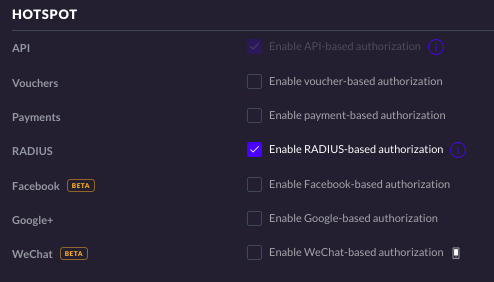
Hotspot
Make the following selection for your hotspot configuration:
- RADIUS: Enable RADIUS-based authorization
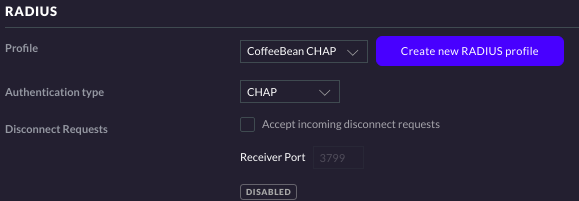
RADIUS
Under the RADIUS menu you will be requested to select a RADIUS Profile. At this point, select the previously created RADIUS profile.
After selecting the RADIUS profile, select the Authentication type to be CHAP.
Access Control
Under this submenu, you will be defining which IPs should be accessible before users authenticate onto your network.
To do so, we’re going to list all IPs to which we need access under the Pre-Authorization Access portion of the list. For the purposes of this guide, leave Post-Authorization Restrictions as default.
Notice that the IPs to be accessed will depend on which kind of authentication you will be implementing for your network. Since these IPs may vary quite a bit over time, CoffeeBean keeps an updated list on its Walled Garden Page.
Note: Do not forget to add CoffeeBean’s IP as it is mandatory for the Portal to be accessible. The IPs to be added will depend on your region and environment.
Overriding UniFi’s Captive Portal
UniFi Network Controller
Download the necessary files from our repository
Identify the site identifier by looking at the dashboard url. Example: https://10.0.0.2:8443/manage/site/axgetkpn/dashboard, in this case the identifier is "axgetkpn". The default site and identifier is "default".
After downloading our files, head to your controller’s directory:
- Linux: /usr/lib/unifi/data/sites/<identifier>/app-unifi-hotspot-portal
- Mac: ~/Library/Application Support/UniFi/data/sites/<identifier>/app-unifi-hotspot-portal
- Windows: Ubiquiti UniFi\data\sites\<identifier>\app-unifi-hotspot-portal
Once you’re in the directory, perform the following steps:
- Rename the index.html file to index.default.html
- Extract our archive file to a temporary directory
- Open the file sid_unifi.js and ensure the sidPortal variable has the link to the portal provided by CoffeeBean (e.g. sidPortal: "https://wifi.socialidnow.com/portals/cbt-ubnt-unifi-lab")
- Copy the downloaded files into the UniFi controller directory
- Restart the UniFi service running on your local machine
UniFi Cloud Key
In case you're using a Cloud Key in your network setup, the location to where the files should be exported is /srv/unifi/data/sites/<identifier>/app-unifi-hotspot-portal
Transfer the downloaded files to the Cloud Key via SFTP.
Customer Parameters
The summary of customer specific parameters is:
- RADIUS Server (primary and secondary)
- IP Address: the RADIUS server IP according to your environment/region
- Password/Shared Secret: the provided RADIUS client secret (Max Length 16 characters)
- Guest Policies
- Landing Page
- Promotional URL: the provided captive portal welcome URL
- Landing Page
- Access Control: get the list of IPs you want to enable to unauthenticated users at our documentation.
- Overriding portal: In the sid_unifi.js file, store the provided captive portal welcome URL in the variable sidPortal