Aruba IAP
Renato.neves (Talk | contribs) (Created page with "The following guide was created using an Aruba wireless network with the following components: * AP: model APIN0205 * Software: Aruba Instant Virtual Controller 6.5.1.0-4.3.1...") |
Renato.neves (Talk | contribs) (→Roles (Walled Garden)) |
||
| Line 20: | Line 20: | ||
Go to "Security > Roles" and create a new role labeled “socialid-pre-auth”. This role will be used as the pre-authentication rule (walled garden) for the captive portal. | Go to "Security > Roles" and create a new role labeled “socialid-pre-auth”. This role will be used as the pre-authentication rule (walled garden) for the captive portal. | ||
| − | For each walled garden domain you want to enable on your captive portal you will need to add the following rule: Allow any to domain <domain.com>. Example: | + | For each [[Walled Garden for the Social Login|walled garden domain]] you want to enable on your captive portal you will need to add the following rule: Allow any to domain <domain.com>. Example: |
* Allow any to domain socialidnow.com | * Allow any to domain socialidnow.com | ||
Revision as of 16:44, 26 September 2017
The following guide was created using an Aruba wireless network with the following components:
- AP: model APIN0205
- Software: Aruba Instant Virtual Controller 6.5.1.0-4.3.1.2_58595
Contents |
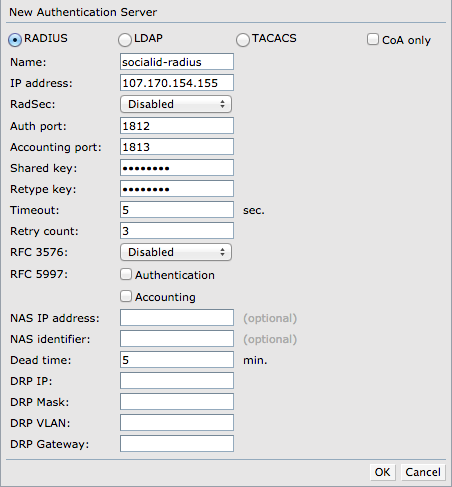
Authentication Server (RADIUS)
Go to "Security > Authentication Servers" and create a new one with the following custom parameters:
- Select RADIUS
- Name: socialid-radius
- IP address: the RADIUS server IP according to your environment/region
- Shared key: the provided shared secret
- Retype key: the provided shared secret
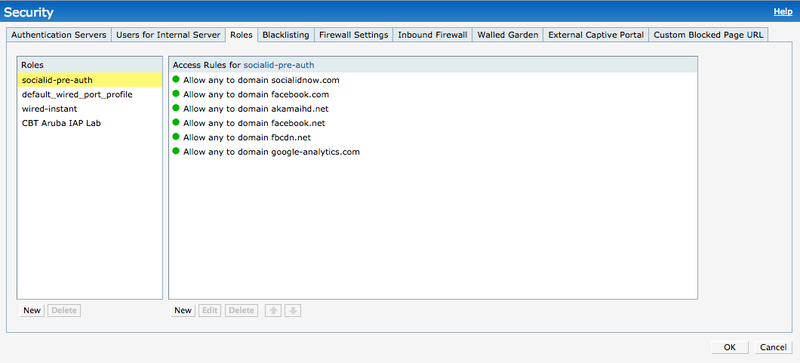
Roles (Walled Garden)
Go to "Security > Roles" and create a new role labeled “socialid-pre-auth”. This role will be used as the pre-authentication rule (walled garden) for the captive portal.
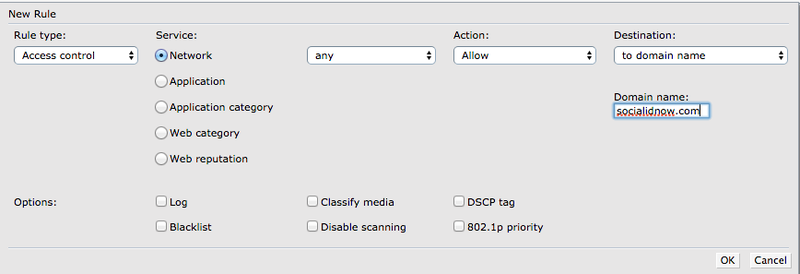
For each walled garden domain you want to enable on your captive portal you will need to add the following rule: Allow any to domain <domain.com>. Example:
- Allow any to domain socialidnow.com
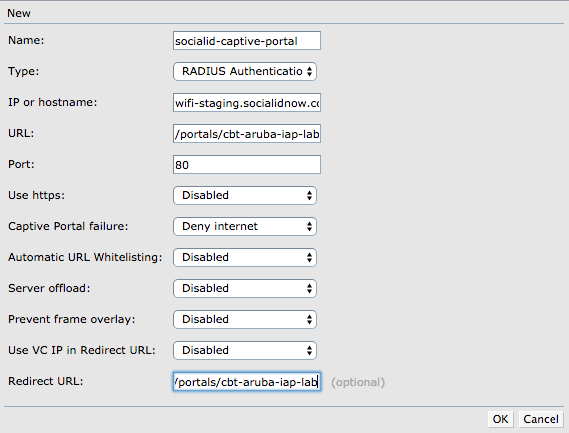
Captive Portal
Go to "Security > External Captive Portal" and create a new one with the following custom parameters:
- Name: socialid-captive-portal
- Type: RADIUS Authentication
- IP or hostname: the provided captive portal hostname (e.g.: wifi.socialidnow.com)
- URL: the provided captive portal URL (e.g.: /portals/cbt-aruba-iap-lab/auth)
- Port: 80
- Use https: Disabled
- Redirect URL: the provided captiv portal redirect URL (e.g.: http://wifi-staging.socialidnow.com/portals/cbt-aruba-iap-lab)
WLAN
Create a new Network with the following settings:
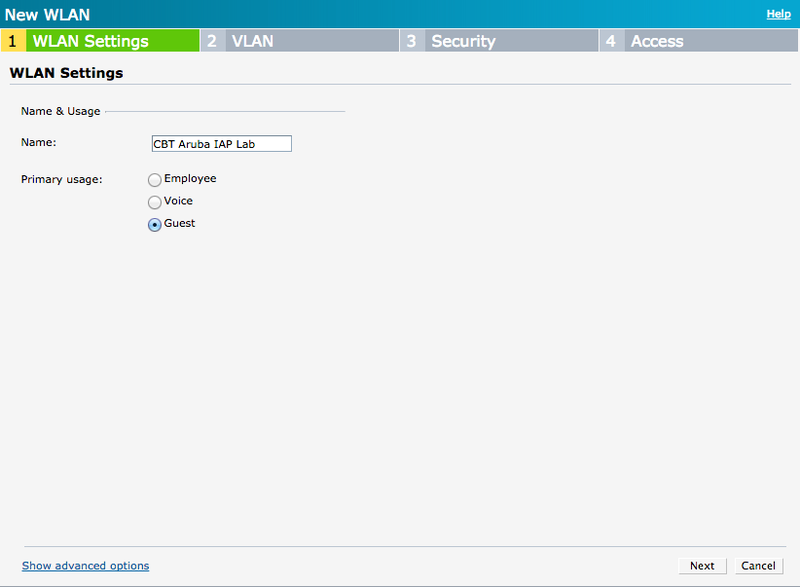
WLAN Settings
- Name: your SSID name
- Primary Usage: Guest
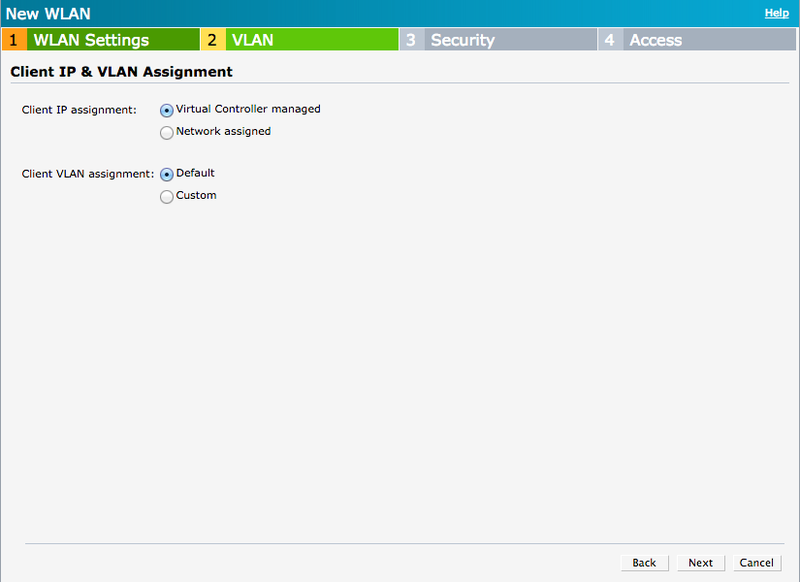
VLAN
- Client IP assignment: Virtual Controller managed
- Client VLAN assignment: Default
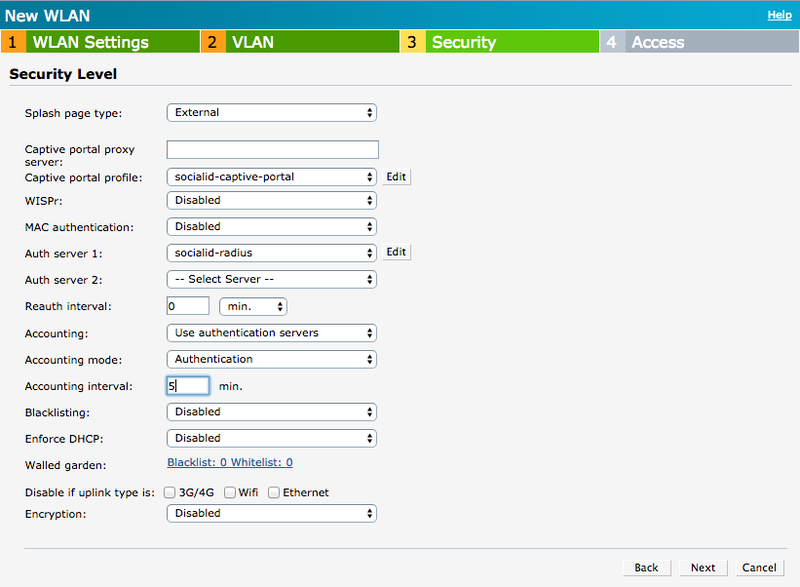
Security
- Splash page type: External
- Captive portal profile: select the captive portal created earlier (e.g.: socialid-captive-portal).
- Auth Server 1: select the authentication server created earlier (e.g.: socialid-radius)
- Accounting: Use authentication servers
- Accounting mode: Authentication
- Accounting interval: 5 min.
- Walled garden: this walled garden does not accept HTTPS based urls, so keep it empty because we are going to implement the walled garden based on Access Rules.
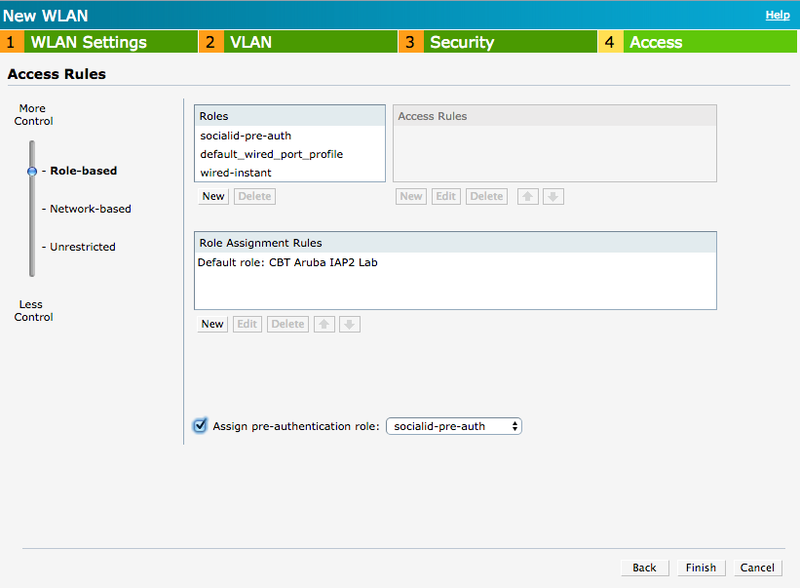
Access
Select “Role-based” control.
Select the pre-authentication role created earlier (e.g.: socialid-pre-auth) and check “Assign pre-authentication role” option.